Anonymization techniques in Workforce Intelligence
Pega Workforce Intelligence™ allows report users to see associate information so they can better understand who is completing the work and what the next steps are for improving how work gets done. Sometimes it is, however, preferable to anonymize the names of associates to expedite the implementation process and to allow for more objective analysis.
The following options are available for user anonymization:
- Customer-provided anonymization – You provide the Workforce Intelligence implementation team a list of associates with the associates’ names already anonymized and mapped to the appropriate team.
- Pega-provided anonymization – You provide the Workforce Intelligence implementation team a list of associates who are mapped to the appropriate teams. The Workforce Intelligence implementation team then updates the names of the associates to be anonymous so associate data is not traceable to an individual.
- Double-blind anonymization – You provide the Workforce Intelligence implementation team a list of associates with the associates’ names already anonymized and mapped to the appropriate team. The Workforce Intelligence implementation team then updates the names of the associates to be anonymous so you cannot trace the data to an individual associate.
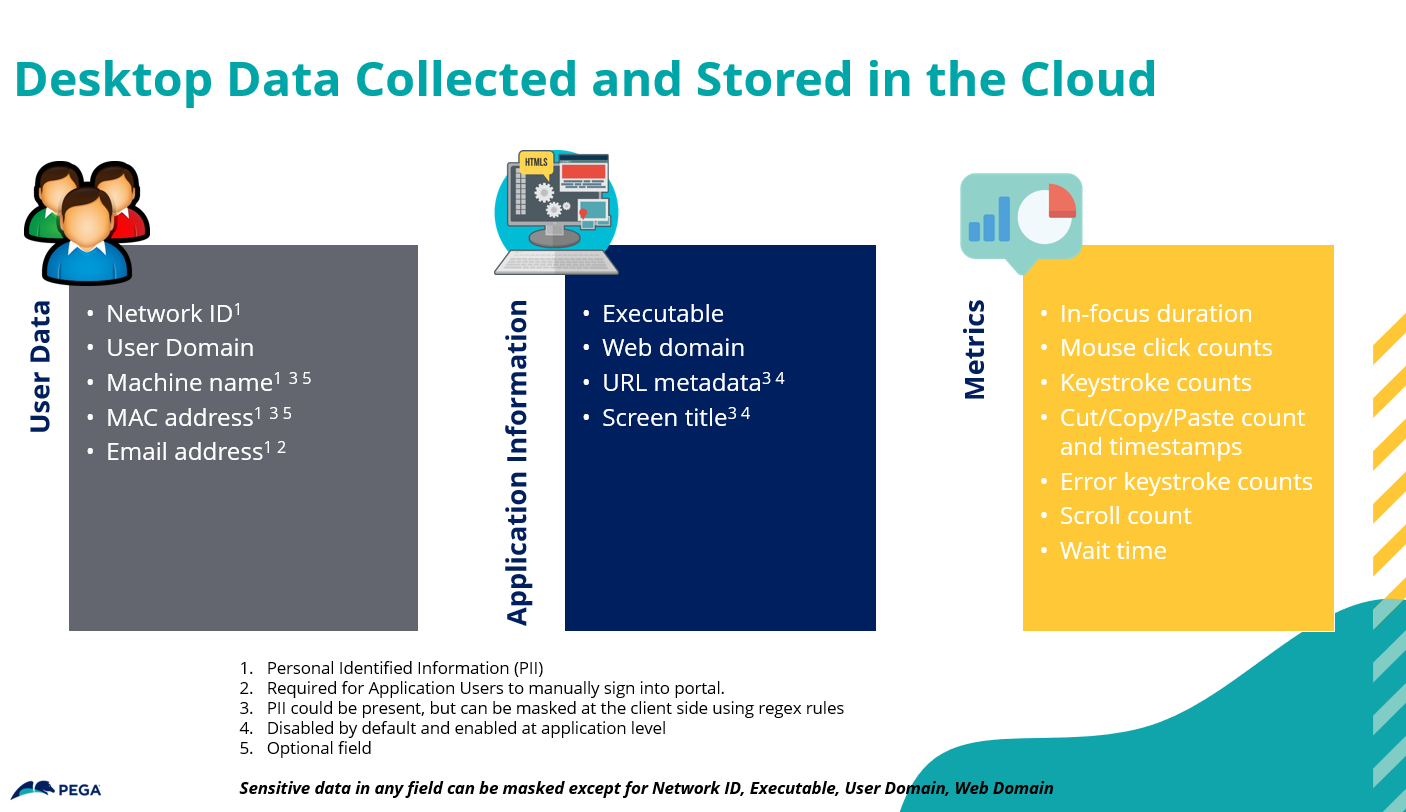
In all of these scenarios, Workforce Intelligence collects the associate’s network login ID. Your Workforce Intelligence administrator can use regular expression (regex) rules to mask all of the other data that Workforce Intelligence collects, except for the Network ID, Executable, Domain, and Web Domain fields. For more information, see the Pega Workforce Intelligence Administration Guide.
In addition to user data, Workforce Intelligence also collects the following types of data and stores it in the cloud:
Previous topic Protection of Personally Identifiable Information in Workforce Intelligence Next topic Screen information captured for Workforce Intelligence
